You have most likely seen news reports about how enterprises are struggling to keep up with an exponential surge in cyberattacks. We have some alarming statistics to highlight:
- On average, there are 56 days between the initiation and detection of a cyber-intrusion.
- While companies detect cyber-intrusion on their own after an average of 30 Days, the investigation took longer than 700 days in 12% of cases.
- If you hope to learn about an incident in your organization from an external party, it will take you about 141 Days (median time). And still, 65% of cyber-attacks go undetected.
The long list of regulators’ demands for compliance with laws like GDPR, CCPA, etc., along with the security operations workload, is increasing the cost of maintaining a healthy and hygienic digital SAP environment. Enterprises running SAP on cloud, especially S/4 HANA, connected applications like SAP Analytics Cloud, SAP Ariba and SAP Concur, etc. on SAP Business Technology Platform (BTP) have a dire need for a single solution that is able to detect internal and external cyber threats and that is agile and easy to operate. Keep in mind that for solutions running on SAP BTP like S/4 HANA, SAP Analytics Cloud, Concur, Ariba etc., logs generated are schematically different from those of conventional ABAP systems.
SIEM platforms have been around for many years and are the backbone of Security Operations Centers (SOCs) for most organizations. The tools are essential for capturing log and event data from critical systems and producing system alerts and real-time dashboards when anomalies are detected. Significant fine-tuning and maintenance is required to ensure SIEM technologies remain alert to the most relevant (and accurate) risks. Conventionally configured SIEM systems typically generate a lot of false positives, noise and redundancy. Moreover, classical SIEM products focus on the infrastructure level and usually can only partly monitor the SAP application level, or not monitor the SAP world at all. A truly robust defense requires a capacity for some autonomous and consistent response devoid of false positives and must derive alarms based on multitude of sources.
Why SAP ETD?
SAP Enterprise Threat Detection overcomes weaknesses of conventional SIEM platforms and perfectly fills functional gaps when it comes to the SAP Solutions that support a company’s cybersecurity.
Framework Core consists of five concurrent and continuous functions: Identify, Protect, Detect, Respond, and Recover. When taken together, these functions provide a high-level, strategic view of the lifecycle of an organization’s management of cybersecurity risks.
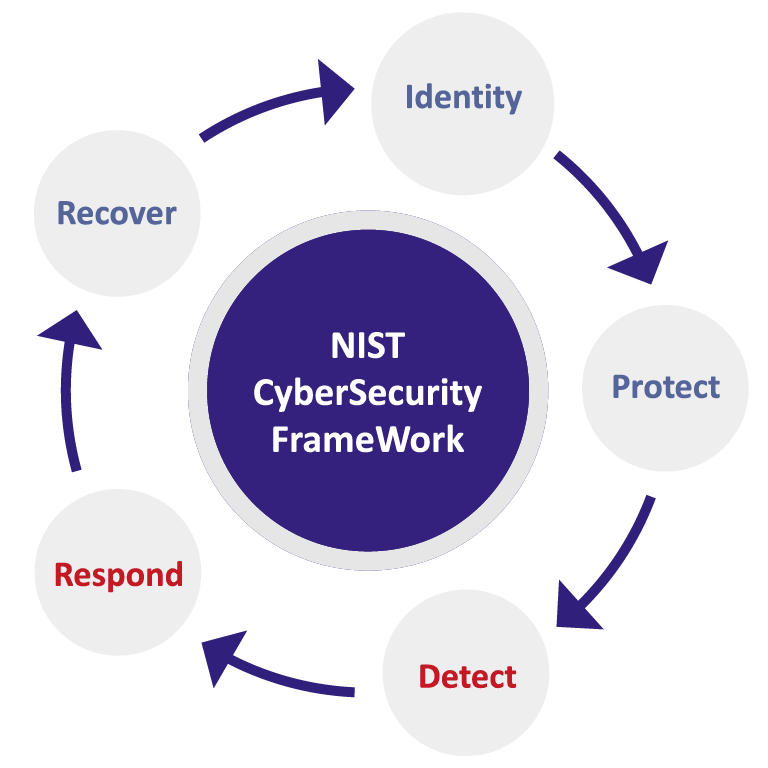
As indicated below, the NIST Cybersecurity Framework is a set of recommendations, based on existing standards, guidelines, and practices, for how organizations can better manage and reduce their cybersecurity risk. The Framework Core consists of five concurrent and continuous functions: Identify, Protect, Detect, Respond, and Recover. When taken together, these functions provide a high-level, strategic view of the lifecycle of an organization’s management of cybersecurity risks.
Solutions like SAP Early Watch Alerts and SAP Focused Run can help you Identify security gaps and to improve the level of Protection; however, these do not allow for real-time threat Detection and Response. SAP ETD is the go-to solution that enables the DETECT and RESPOND control requirements of the NIST Cybersecurity Framework.
SAP ETD promises to reshape cumbersome cybersecurity event detection and operations, time-consuming incident handling and substantial cybersecurity spending by
- Managing Logs from different SAP systems on cloud, on premise and including non-SAP systems.
- Using pre-delivered threat patterns in SAP ETD developed from years of auditing experience and feedback from multiple customers.
- Processing billions of SAP Log records (Power of SAP HANA) to monitor, collect and correlate security events generated within the SAP IT infrastructure, SAP cloud platforms and (if applicable) within the application layers, to detect security incidents and threats for all SAP lines of business.

SAP ETD provides real-time threat visibility into complex SAP landscapes by deriving meaningful insights from variety of (unfiltered, normalized, readable) Logs for SAP Netweaver S/4 Logs (System, SAL, HTTP Server, RFC Gateway, SOAP Based Webservices log), HANA DB logs, SAP BTP (Neo+Cloud Foundry) logs, etc.
With SAP ETD, real-time occurrence of a log event spanning different log types leads to a pattern being evoked, which generates alarms visualized in a simple & intuitive manner. Please refer to the simplified visualization example for a cybersecurity attack below.

A detection pattern in SAP ETD is defined on Users, Systems, Networks, and Hostnames. Here are some pattern examples for SAP NW based systems:
| Risk Level | Pattern | Description |
|---|---|---|
| High Risk | Pattern A | User A Unlocking a critical HR Transaction, Deactivating Audit Log and changing Salary Data in SAP System A |
| Medium Risk | Pattern B | User B on internet accessing trade secrets in SAP system B in Corporate Network |
| Low Risk | Pattern C | User A Deactivating Critical Audit Log Event in SAP System A |
| Low Risk | Pattern D | Unlocking SAP Transaction |
| High Risk | Pattern E | Logon with SAP Standard Users |
If you are interested in learning how you can deploy SAP ETD as a vital part of your organization’s cyber defense strategy, connect with us for a demo/session.
